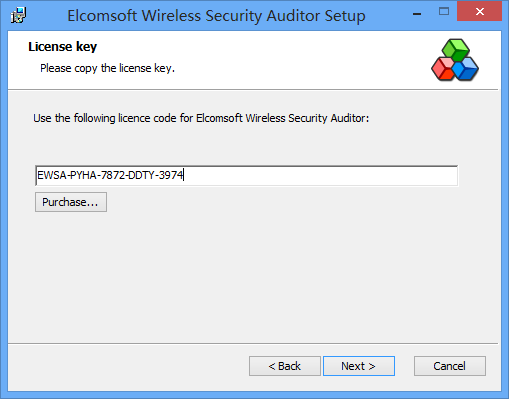
Elcomsoft Wireless Security Auditor Klyuch
Free download program adim adim turkce pdf converter. Turkish View all editions and formats Rating: Be the first to review this item Amazon Bestsellers Rank: Milet Publishing Ltd June 14, Language: Uguumur Ugm marked it as to-read Sep 22, ComiXology Thousands of Digital Comics. I’d like to read this book on Kindle Don’t have a Kindle? Customer reviews There are no customer reviews yet. ADIM ADIM TURKCE EBOOK The E-mail message field turke required.
Elcomsoft Wireless Security Auditor can simulate attacks from the inside by automatically importing saved password hashes as retrieved by Elcomsoft Proactive System Password Recovery. This kind of attacks allows determining how secure your wireless network is to insider attacks.
This is a detailed tutorial on how to use EWSA to crack a WPA or WPA2 secured WiFi network on Windows. Complete with AirPcap monitor and handshake capturing also on windows. No need to use linux at all, however you are not able to deauthenticate connected clients to get handshake faster, so you must wait until client connects into AP if you're doing this on windows. Using linux, you can deauthenticate any connected client and get handshake instantly. On this video I have replicated the connecting client to get the handshake on demand. EWSA is available @ elcomsoft.com AirPcap is available @ riverbed.com (special thanks goes to Elcomsoft for providing me one) HOW TO CAPTURE HANDSHAKE in BackTrack5 linux: HOW TO EXTRACT HANDSHAKE FROM BIG FILE: 1. You can use Cain - 2.
Free free download learning rhino 5 tutorial dvd video training 2016 and full v. This course comes complete with a full set of working files so you can work with the very same files that the author uses in the training video. By the conclusion of this computer based training course, you will be capable of creating beautiful 3D and 2D models.
You can use tshark on linux: The following command will extract all handshake and beacon packets from the capture file and saves into new file: tshark -r [input file name] -R 'eapol wlan.fc.type_subtype == 0x08' -w [output file name] The -R option can be changed to suit whatever filter you want to use for example if you wanted to grab all the eapol packets and only the beacons for a specific essid: tshark -r [input file name] -R 'eapol wlan_mgt == 00:14:6C:7E:40:80' -w [output file name] hacking.